
Clickjacking is the short form of click hijacking. This vulnerability is used by an attacker to collect an infected user’s clicks. The attacker can force the to do all sort of things from adjusting the user’s computer settings to unwittingly sending the user to Web sites that might have malicious code. Now how attacker can adjust user’s computer setting? attacker uses multiple transparent or opaque layers to trick a user into clicking on a button or link on another page when they were intending to click on the the top level page. Thus, the attacker is "hijacking” clicks meant for their page and routing them to other another page, most likely owned by another application, domain, or both.
Clickjacking is a malicious script, also known as UI Redressing which takes over the links displayed in the Internet browser for various web pages. When this happens, the user is taken to a site which is unintended when he tries to lick on that link. In other words, clickjacking simply is an embedded script or code which can click on a button that appears to perform another function, without the user’s knowledge.
The term "clickjacking” was coined by Jeremiah Grossman and Robert Hansen in 2008. The exploit is also known as UI redressing.

Sometimes a user is unaware of what has just happened or in some case, a user can immediately detect it. There are a few things which everyone ought to be aware about this menace that can create havoc.
1. Clickjacking happens when a website is embedded with a malicious program. This program apparently hovers under the unaware user’s mouse, and if the user clicks the mouse on a page or link, a new web site appears or downloading of software takes place.
2. Its a malicious script which can virtually run on any website without the owner being aware or having the ability to stop it. These attacks have been a major cause of concern for many big companies and major websites like Facebook.
3. Making the user believe that he is on the company website, clickjacking can create a mirror site and collect personal information.
4. Except very few browsers which are not based on graphics are immune from the clickjacking software.
5. Clickjacking can steal personal data, like social security numbers, credit card and bank information.
6. This malicious script can work without the knowledge of the user, install a number of software applications in a computer. They could be harmful viruses, adware or software which is more so harmful for the computer.
7. A new clickjacking software has been disclosed which can be used to spy on your webcam and microphone in Adobe’s Flash software. Adobe’s Flash software is vulnerable as it enables the clickjacking to gain access of the user’s microphone and webcam. While the user visits a web page, unknown to him, the target application waits invisible and loaded while it floats the invisible allow button. When the user click on the flash button, the invisible allow button receives your click actually. The Flash application is now accessed with full permission and may even stream from your microphone and webcam to a server for recording.
The Clickjacking attack allows to perform an action on victim site on visitor’s behalf.
Many sites were hacked this way, including Twitter and Facebook (both fixed).
Clickjacking
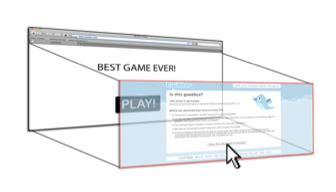
The overall idea is simple.
1. A visitor is lured to evil page. No matter how. "Click to get 1000000$” or whatever.
2. The evil page puts a "get rich now” link with z-index=-1.
3. The evil page includes a transparent iframe from the victim domain, say facebook.com and positions it so that "I like it” button is right over the link.
Here’s how it looks (half-transparent iframe for demo purposes):
A click on the link actually happens on the iframe. Bingo! If the visitor is logged into facebook (and most of time he is), then facebook.com receives the click on behalf of the visitor.
On Twitter, it was the "Follow” button.
Same code, but transparent iframe (click to see the victim button pressed):
Countermeasure of Clickjacking :
NoScript: This is the best prvention aginst Clickjacking. It is a firefox addon and prevent users from clicking invisible click.
GuardedID: It is a commercial product which provides client-side clickjack protection for users of IE or Firefox without interfering with the operation of legitimate iFrames
Comitari Web Protection Suite: Comitari provides client side protection against ClickJacking (aka UI Redressing) attacks. Installed as browser add-on






