Cache poisoning (Domain Name System Poisoning or DNS cache poisoning)
Cache poisoning, also called domain name system (DNS) poisoning or DNS cache poisoning, is the corruption of an Internet server's domain name system table by replacing an Internet address with that of another, rogue address. When a Web user seeks the page with that address, the request is redirected by the rogue entry in the table to a different address. At that point, a worm, spyware, Web browser hijacking program, or other malware can be downloaded to the user's computer from the rogue location
Cache poisoning can be transmitted in a variety of ways, increasing the rate at which rogue programs are spread. One tactic is the placement of compromised URLs within spam e-mail messages having subject lines that tempt users to open the message (for example, "Serious error in your tax return"). Images and banner ads within e-mail messages can also be vehicles by which users are directed to servers that have been compromised by cache poisoning. Once an end user's computer has been infected with the nefarious code, all future requests by that user's computer for the compromised URL will be redirected to the bad IP address -- even if the "victim" server resolves the problem at its site. Cache poisoning is particularly dangerous when the targets are well-known and trusted sites, such as those to which browsers are pointed when automatic virus-definition updates are performed.
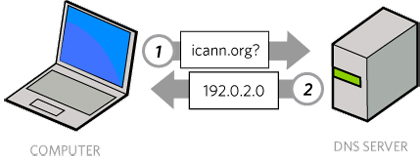
A DNS runs on DNS protocol that translates web address into its respective IP address. Now DNS poisoning or DNS spoofing is technique by which an attacker provides wrong IP address to DNS server for misdirecting users to fake websites. Following are types of DNS poisoning, in future post we will cover them briefly,
- Intranet DNS Spoofing/Poisoning
- Internet DNS Spoofing/Poisoning
- Proxy Server DNS Spoofing/Poisoning
- DNS Cache Spoofing/Poisoning
Cache poisoning differs from another form of DNS poisoning, in which the attacker spoofs valid e-mail accounts and floods the inboxes of administrative and technical contacts. Cache poisoning is related to URL poisoning. In URL poisoning, also known as location poisoning, Internet user behavior is tracked by adding an identification (ID) number to the location line of the browser that can be recorded as the user visits successive pages on the site.






