The attack works by first detecting that the tab the page is in does not have focus. Then the attacking script can change the tab favicon and title before loading a new site, say a fake version of gmail or orkut, in the background.
Even scarier, the attack can parse through your history to find sites you actually visit and impersonate them.
Because most of us trust our tabs to remain on the page we left them on, this is a particularly difficult attack to detect. As Raskin writes, "as the user scans their many open tabs, the favicon and title act as a strong visual cue — memory is mailable and moldable and the user will most likely simply think they left [the] tab open.”
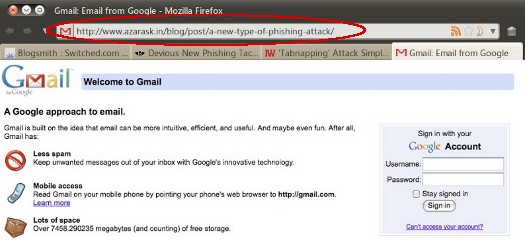
The only clue that you’re being tricked is that the URL will be wrong.






