

Kevin David Mitnick (born August 6, 1963) is a computer security consultant and author. In the late 20th century, he was convicted of various computer- and communications-related crimes. At the time of his arrest, he was world-famous as the most-wanted computer criminal in the United States.Mitnick gained unauthorized access to his first computer network in 1979, at 16, when a friend gave him the phone number for the Ark, the computer system Digital Equipment Corporation (DEC) used for developing their RSTS/E operating system software. He
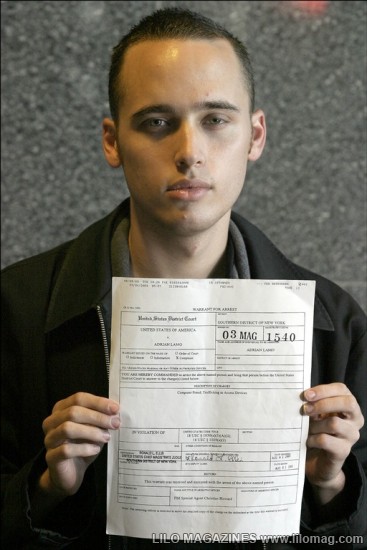
After a warrant was issued for his arrest, Mitnick fled, becoming a fugitive for two and a half years. According to the U.S. Department of Justice, Mitnick gained unauthorized access to dozens of computer networks while he was a fugitive. He used cloned cellular phones to hide his location and, among other things, copied valuable proprietary software from some of the country’s largest cellular telephone and computer companies. Mitnick also intercepted and stole computer passwords, altered computer networks, and broke into and read private e-mail. Mitnick was apprehended in February 1995 in North Carolina. He was found with cloned cellular phones, more than 100 clone cellular phone codes, and multiple pieces of false identification.
4 ) Kevin Poulsen

Poulsen’s best known hack was a takeover of all of the telephone lines for Los Angeles radio station KIIS-FM, guaranteeing that he would be the 102nd caller, and winning a Porsche 944 S2. In June 1994, Poulsen pleaded guilty to seven counts of mail, wire and computer fraud, money laundering, and obstruction of justice, and was sentenced to 51 months in prison and ordered to pay $56,000 in restitution. It was the longest sentence ever given for hacking up to that time. He also later pleaded guilty to breaking into computers and obtaining information on undercover businesses run by the FBI.

Now we have. . .
White Hat Hackers -
White hat hackers, also known as ethical hackers, or white knights, are computer security experts, who specialize in penetration testing, and other testing methodologies, to ensure that a company’s information systems are secure. Such people are employed by companies where these professionals are sometimes called "sneakers.” Groups of these people are often called tiger teams or red teams. These security experts may utilize a variety of methods to carry out their tests, including social engineering tactics, use of hacking tools, and attempts to evade security to gain entry into secured areas.
1 ) Stephen Wazniak
Stephen Wazniak, one of the founders of Apple Computer and a long-time hacker hero, recalled the days when a young hacker could twiddle the phone system and make a free phone call to the pope without fear that a goofy prank would turn into an international incident. Steve Wozniak got the first
2 ) Tim Berners-Lee

Berners-Lee is famed as the inventor of the World Wide Web, the system that we use to access sites, documents and files on the Internet. He has received numerous recognitions, most notably the Millennium Technology Prize. While working with CERN, a European nuclear research organization, Berners-Lee created a hypertext prototype system that helped researchers share and update information easily. He later realized that hypertext could be joined with the Internet. Berners-Lee recounts how he put them together: "I just had to take the hypertext idea and connect it to the TCP and DNS ideas and "ta-da!” the World Wide Web.”
Since his creation of the World Wide Web, Berners-Lee founded the World Wide Web Consortium at MIT. The W3C describes itself as "an international consortium where Member organizations, a full-time staff and the public work together to develop Web standards.” Berners-Lee’s World Wide Web idea, as well as standards from the W3C, is distributed freely with no patent or royalties due.
3 ) Linus Torvalds
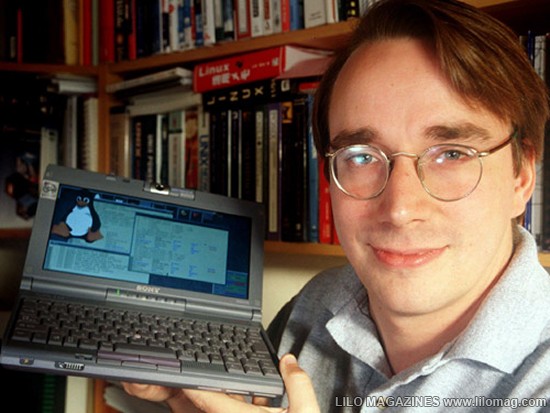
In 1991 Linus Torvalds was a college student at the University of Helsinki. Starting with the basics of a Unix system, he wrote the kernel — original code — for a new system for his x86 PC that was later dubbed Linux (pronounced linn-ucks). Torvalds revealed the original source code for free — making him a folk hero among programmers — and users around the world began making additions and now continue to tweak it. Linux is considered the leader in the practice of allowing users to re-program their own
4 ) Richard Stallman
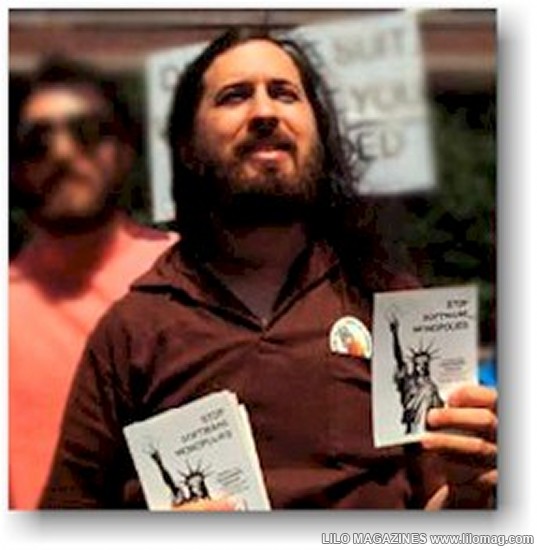
Richard Matthew Stallman (born March 16, 1953), often abbreviated "rms”,[1] is an American software freedom activist, and computer programmer. In September 1983, he launched the GNU Project to create a free Unix-like operating system, and has been the project’s lead architect and organizer. With the launch of the GNU Project, he initiated the free software movement and, in October 1985, set up the Free Software Foundation. Stallman’s life continues to revolve around the promotion of free software. He works against movements like Digital Rights Management (or as he prefers, Digital Restrictions Management) through organizations like Free Software Foundation and League for Programming Freedom. He has received extensive recognition for his work, including awards, fellowships and four honorary doctorates.
5 ) Tsutomu Shimomura
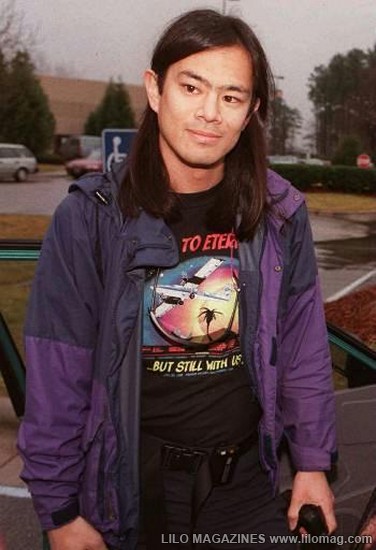
Shimomura reached fame in an unfortunate manner: he was hacked by Kevin Mitnick. Following this personal attack, he made it his cause to help the FBI capture him. Shimomura’s work to catch Mitnick is commendable, but he is not without his own dark side. Author Bruce Sterling recalls: "He pulls out this AT&T
The article, "SDSC Computer Experts Help FBI Capture Computer Terrorist” recounts how Shimomura pinpointed Mitnick’s location. Armed with a technician from the phone company, Shimomura "used a cellular frequency direction-finding antenna hooked up to a laptop to narrow the search to an apartment complex.” Mitnick was arrested shortly thereafter. Following the pursuit, Shimomura wrote a book about the incident with journalist John Markoff, which was later turned into a movie.






