Cracking Windows User Account password
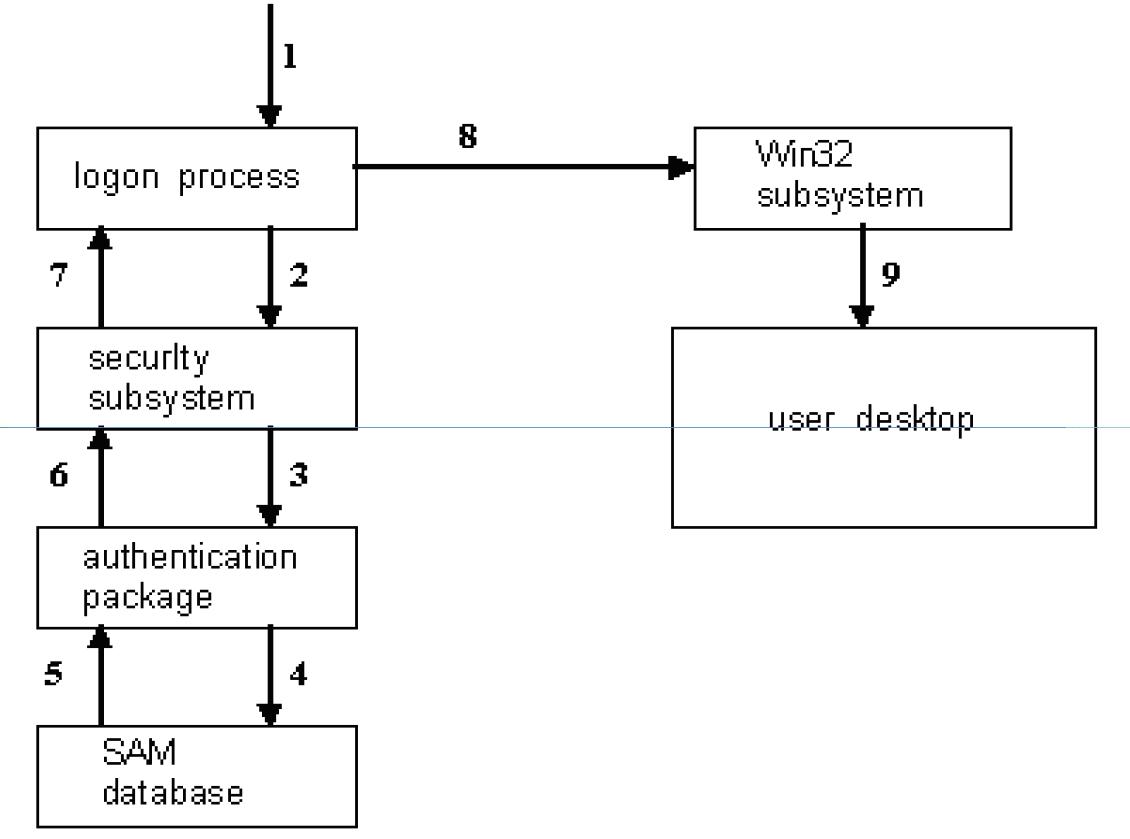
v Passwords are Stored and Transmitted in an encrypted form called a Hash. When a User logs on to a system and enters a password, a hash is generated and compared to a stored hash. If the entered and the stored hashes match, the user is authenticated (This is called the Challenge/Response).
v Passwords may be cracked manually or with automated tools such as a Brute-force method or the Rainbow Table attack.
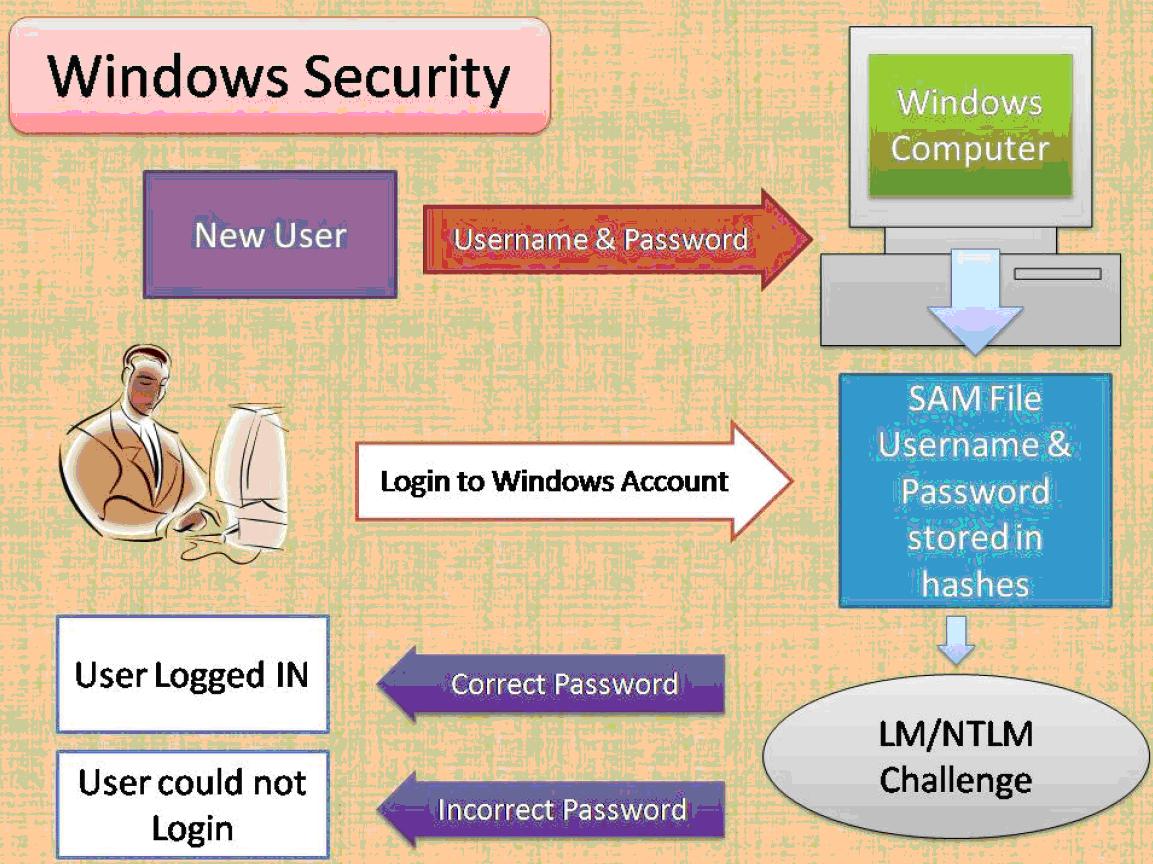
v In this if we put the password and windows vey the password we entered on teen with the file in which the password is stored of ours.
v This is stored in a file named SAM
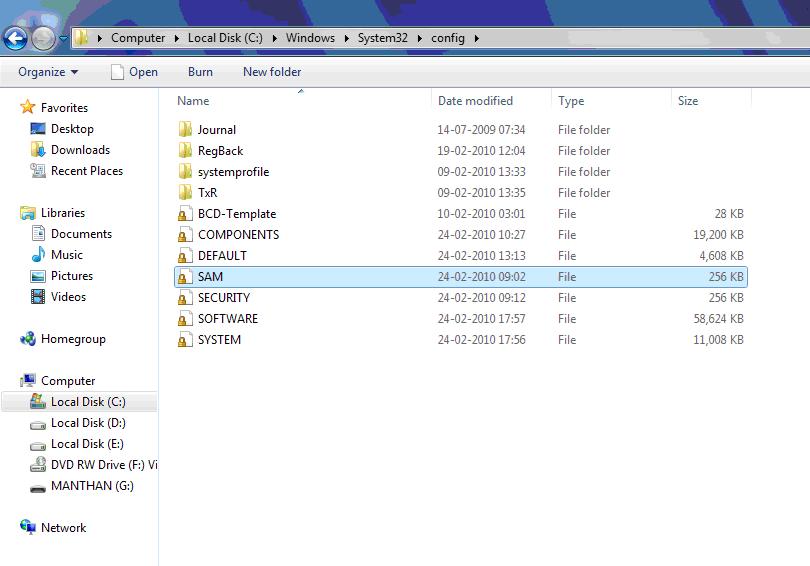
v It is shown in the picture above.
v Now we need to attack this file.
v For this we need to open this file but it is not possible as it is in process by the computer from its start up.
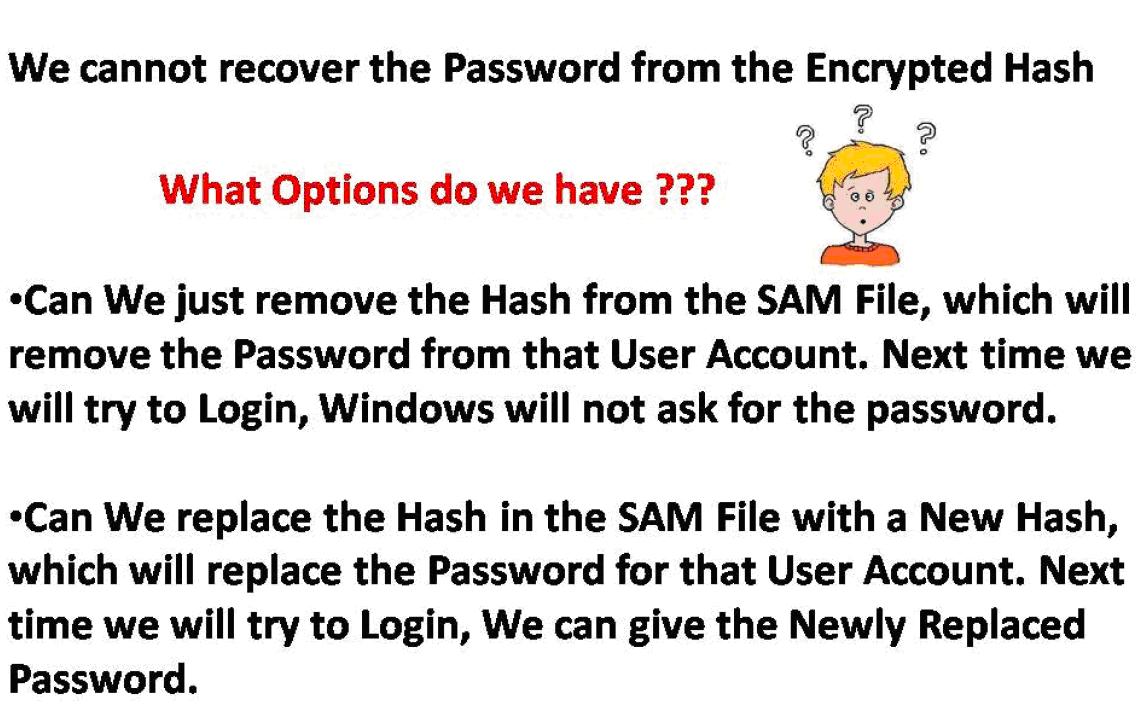
v And we suppose that the file opens then also we cannot see the passwords stored in it because they are encrypted in the form of HASHES.
v And they and not be decrypted. Ad it is the hardest encryption done and decryption is not easy.
v But it is not impossible.
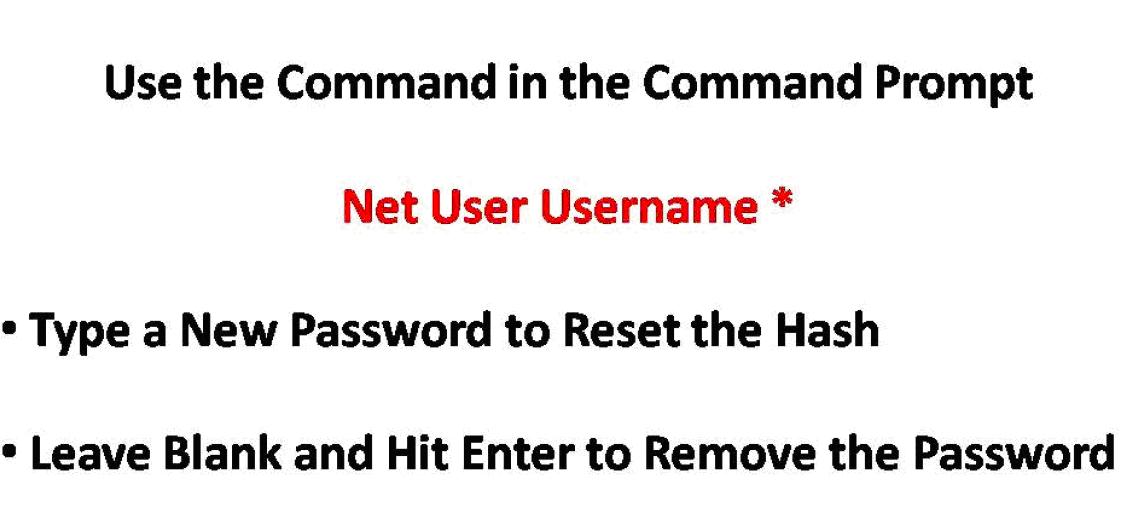
v We Need a Bootable CD named Hiren boot and Can Crack the Password.
But Another Attack –
v Go to C:\Windows\System32\
v Copy the File cmd.exe to desktop and rename it to sethc.exe
v Now copy the file sethc.exe to C:\Windows\System32\ and will give an error, give that error YES. And replace it.
v Now You Are Done.
v Now At the Login Screen Press SHIFT Key 5 times and a beep Sound will come and Command prompt will open.
v In the command prompt type "explorer.exe” and Hit Enter a desktop will open in the tab mode.Use The Computer Unlimited….






